What Is Identification, Authentication and Authorization?

Updated March 2026
In more analog days, hard copies of official government documents, physical identification cards and biometric information like fingertips were all viable ways to make sure a person was who they claimed to be. The digital age with its myriad online transactions, however, requires new ways to identify, authenticate and authorize a person's identity.
Let's take a closer look at identification, authentication and authorization and why each process is increasingly important in the modern world.
How Identity Verification Works
Digital identity verification isn't a single event; it's a layered process that builds trust through three distinct but interconnected steps. Each phase serves a specific purpose in confirming that users are who they claim to be and should have access to what they're requesting.
Think of it like entering a secure building: you first show your ID at the front desk (identification), prove it's really you through additional verification (authentication), then receive specific permissions based on your role (authorization). In digital transactions, this same principle applies — whether you're accessing a bank account, signing a mortgage document, or authorizing a wire transfer.
The Importance of Identification
In most digital transactions, identification is the step where users prove their identity by providing a name, email address, phone number or username.
Identification is the first step in confirming a person's identity and must happen before authentication and authorization. Users can also provide more information, like a government-issued photo, ID, or social security number, to further identify themselves.
Identification happens in the initial setup stage of accounts and services. A username and password typically identify a person each time they access that account or service.
However, it can be challenging in digital environments to verify identification simply by receiving personally identifiable information and usernames and passwords. A stolen wallet or hacked email account is also enough for someone to attempt to steal an identity.
Given these risks, identification is simply the first step to establishing the baseline for the authentication process.
Common Identity Verification Challenges
Digital identification faces unique vulnerabilities that traditional, in-person verification doesn't encounter. Fraudsters can easily obtain personal information through data breaches, social engineering, or even purchasing it on the dark web. A social security number, address, and date of birth — the traditional markers of identity — are no longer sufficient proof in our connected world.
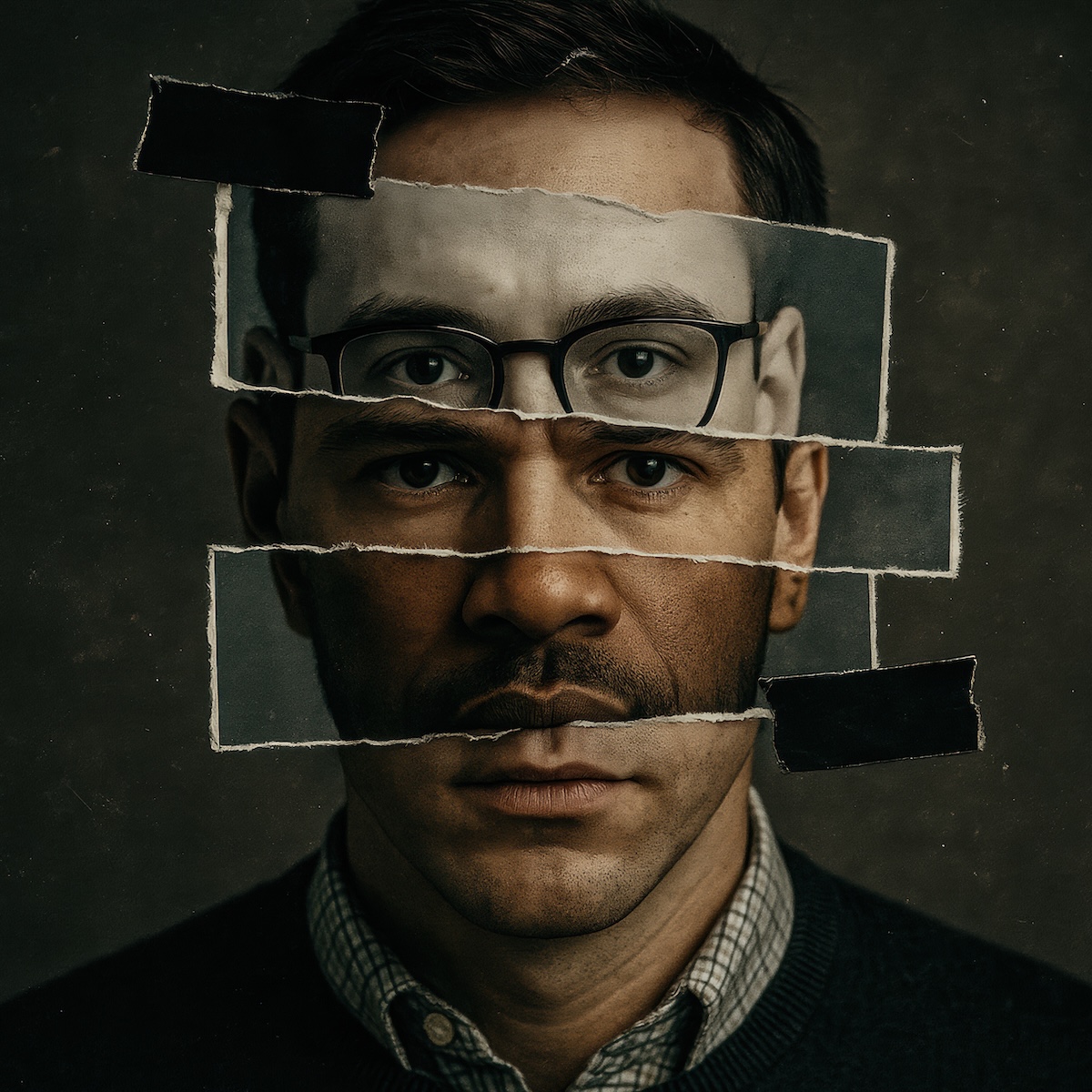
Document forgery has become increasingly sophisticated, with AI-generated IDs and deepfake photos making it difficult to distinguish authentic credentials from fabricated ones. Even legitimate documents can be stolen and used by someone else, creating a scenario where the identification appears valid but belongs to the wrong person.
Forms of Identification For Authentication
Depending on the transaction's requirements, identification can require one or all of the following:
What you know
Information that only the person in question would easily know, including passwords, personal identification numbers (PINs), maiden names or answers to security questions.
What you have
Possessions that are unique to a specific person, like keys, badges or swipe cards.
What you are
As the most secure form of identification, biometric information is immune to theft or replication and can definitively prove identity. This information includes things like fingerprints or a facial scan.
The Importance of Authentication
Authentication requires users to prove they are still the person they claimed to be during the identification phase.
In 2021, the FTC received more than 2.8 million reports of fraud, resulting in over $5.8 billion in losses. If identification was the only barrier between access to an account or a system, these fraud and identity theft instances would be even more rampant. Authentication provides a layer of protection beyond identification to help users keep their accounts and their identities secure.
Following basic identification, authentication initiates a match between the user's previously provided information. Increasingly, authentication systems ask for a one-time verification code sent to an email address or phone number, even if the user's provided details and stored information match. Authorization requires both identification and authentication.
When Authentication Fails: Security Vulnerabilities
Authentication systems aren't foolproof — and understanding where they break down is crucial for organizations handling sensitive transactions. SIM swapping attacks can compromise phone-based authentication, while email account takeovers can bypass email verification codes. Even biometric systems face challenges from spoofing attempts using photos, videos, or synthetic fingerprints.
The rise of AI-generated content creates new authentication vulnerabilities. Deepfake technology can now create convincing video calls that fool facial recognition systems, while voice cloning can bypass phone-based verification. These emerging threats require authentication systems to evolve beyond traditional methods and incorporate liveness detection, behavioral analysis, and real-time fraud monitoring.
Methods of Authentication
Password-based authentication
Passwords are the most common method of authentication. Optimal protection requires using many varied passwords using different strings of letters, numbers and characters. However, many people use the same or similar passwords across accounts, which leaves them vulnerable to phishing and password breaches. Malicious entities can easily bypass password protection if they can access the user's email account or a previously used password. In short, passwords alone are not sufficient to provide account protection.
Multi-factor authentication
A safer authentication method involves multi-factor authentication (MFA), which requires using more than one form of authentication, like a Captcha request or a security code sent to your email or phone as an SMS message. MFAs have their own drawbacks, as some users may lose access to a previous email or phone number, effectively locking them out of their account without intervention.
Certificate-based authentication
Essentially, certificate-based authentication (CBA) uses a digital certificate to identify a user, device or machine before providing access to an application, network or other resource. This form of authentication is more secure because it's based on both what the user has (the digital certificate) and what they know (their password).
Biometric-based authentication
Biometric-based authentication relies on individuals' unique biological characteristics to authenticate their identity. Methods like facial recognition, fingerprint or eye scanning and voice recognition provide a high level of security with minimal disruption. When paired with multi-factor authentication, this method provides an additional layer of security. However, biometric-based authentication does present privacy concerns — and ethical questions for some.
Token-based authentication
Token-based authentication simplifies the authentication process for recognized users. After entering a username and password, a user can access protected systems without providing credentials again.
The Importance of Authorization
Authorization grants users access, rights and privileges to a service, account, or system based on previously secured identification and authentication.
Identification and authentication validate a person's identity, but authorization ensures the person in question should have access to the system or resource.
Authorization gives users rights and privileges after identifying, authenticating and authorizing them. It secures sensitive resources in a system and protects individual users from unauthorized access to their accounts or information.
Access Control in High-Risk Environments
Authorization becomes critical when stakes are high — think wire transfers, legal document signing, or account ownership changes. In these scenarios, confirming identity isn't enough; you need to verify that the authenticated person has the legal right to authorize the specific action they're requesting.
Effective authorization systems implement role-based access controls, time-sensitive permissions, and transaction limits based on risk levels. They also maintain detailed audit trails that track not just who accessed what, but when, from where, and what actions they performed. This creates defensible records that can stand up to legal scrutiny if disputes arise.
Types of Authorization Methods
API keys
An API key is a secret code that gets you inside a system or resource, essentially acting like an ID card to assign proper permissions and track data usage. In more technical terms, it's a string of characters used to identify and authorize an application or user who requests the service of an API (application programming interface).
Basic auth
Basic auth is akin to providing a key in the form of user credentials to access an online account. Although this process is straightforward, it can leave your credentials and, eventually, your online account vulnerable.
HMAC
HMAC stands for Keyed-Hashing for Message Authentication. Because it uses cryptography keys to enforce integrity and authenticity, HMAC is similar to digital signatures. Secure file transfer protocols like FTPS, SFTP and HTTPS use HMAC to ensure data integrity.
OAuth
OAuth uses authorization tokens vs. a password to connect an app to a user account. It allows users to give other websites or applications access to their information without resupplying passwords.
Key Differences: Identification vs Authentication vs Authorization
While these three concepts work together, understanding their distinct roles helps organizations design more secure systems:
Identification answers "Who are you?" — it's about claiming an identity through usernames, email addresses, or ID documents. This is the starting point but offers the least security on its own.
Authentication answers "Can you prove it?" — it verifies that you are actually the person you claimed to be during identification. This is where passwords, biometrics, and verification codes come into play.
Authorization answers "What can you do?" — it determines what actions, resources, or information you can access based on your proven identity and assigned permissions. Even authenticated users may not be authorized for every action.
The key insight: all three must work together. Strong identification without proper authentication leaves you vulnerable to impersonation. Solid authentication without appropriate authorization can grant excessive access. And robust authorization built on weak identification creates a false sense of security.
Notarize Can Help Businesses Identify and Authenticate Online Notarizations
Many applications and processes require consumers to identify, authenticate and authorize their digital identity.
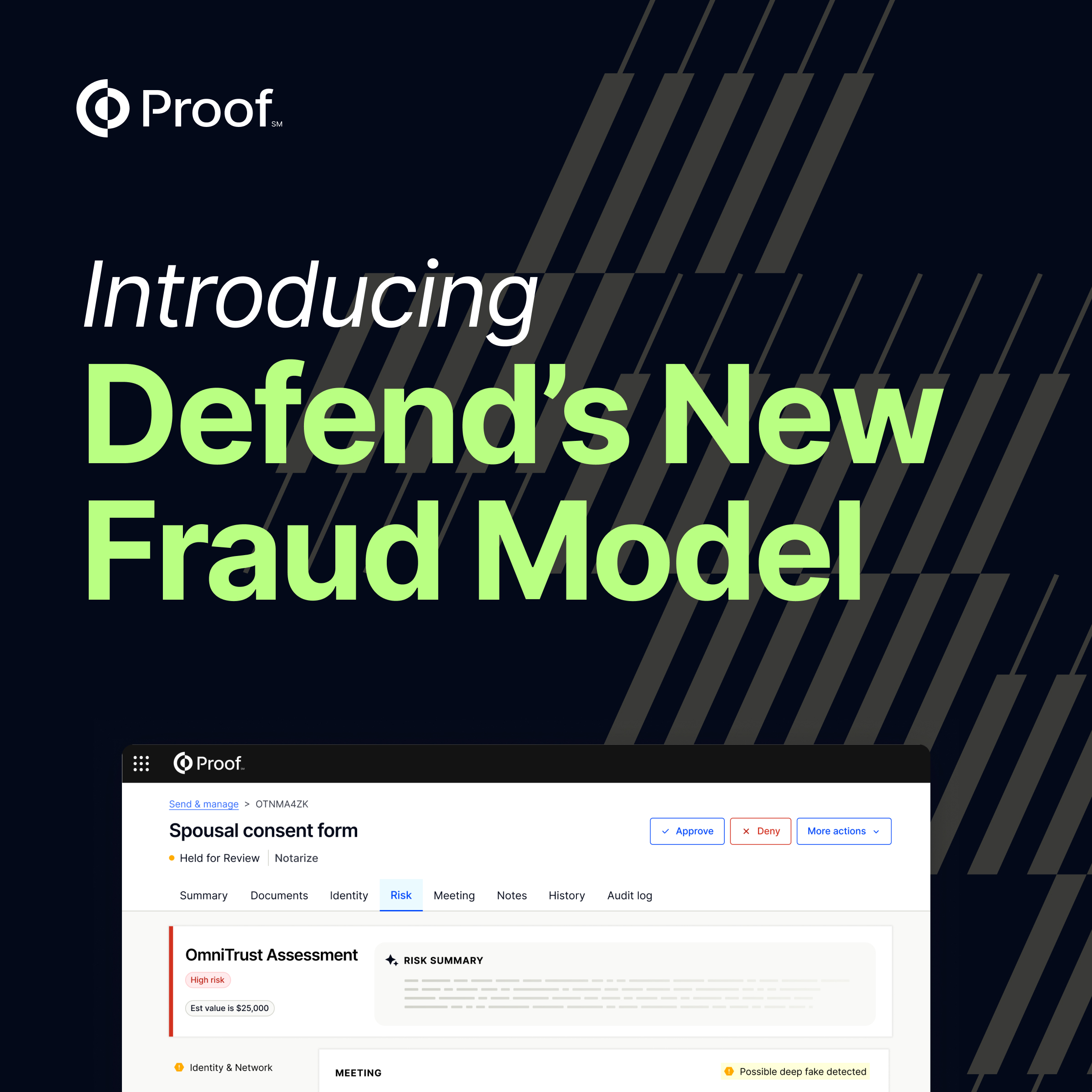
Notarize uses dynamic knowledge-based authentication and database-driven information to confirm a person's digital identity to prevent fraudulent notarizations and secure online notarizations for business.


























.jpg)
























































.png)

.jpg)